Keeping Your Data Safe
Reqi is built on Azure Cloud with enterprise-grade security at every layer. Your requirements data is encrypted, zone-redundant, and hosted in an Australian data centre — with strict access controls, continuous monitoring, and a commitment to compliance.
Data Security
Secure infrastructure, third-party audits, and industry-standard certifications including ISO 27001 and SOC-2 compliance through Azure Cloud.
Compliance
We help you meet your compliance obligations while continuously strengthening our own certifications and security posture.
Privacy
Your data is yours. Our policies and processes are designed to protect your information and respect your privacy at every step.
Data Security
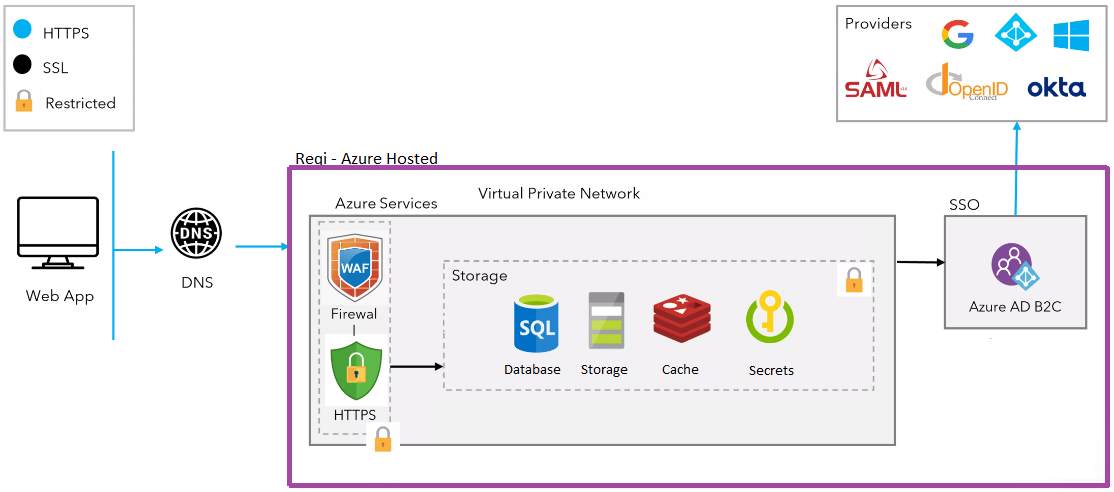
Reqi is built on Azure Cloud, which is subject to numerous third-party security audits and follows the highest industry standards in information and operational security compliance certifications such as ISO 27001 and SOC-2.
Our servers are located in an Australian data centre, ensuring compliance with data protection schemes of this region. All data is encrypted at rest and in transit, and we use Azure Web Application Firewall to further enhance security.
Data Residency
Reqi uses Azure Cloud services to store client data, which adheres to a strict decommissioning policy to ensure data security and compliance. Data is deleted immediately when a client's services are decommissioned, and we also offer an option for automatic data purge on regular intervals if requested.
As part of audit tracing, each user's working data is stored with full traceability, ensuring your data is always accounted for and protected.
Reliability
Reqi targets 99.9% uptime with constant performance and load testing, and 24/7 monitoring of services with automated alerts in case of any downtime.
Security at every stage: We perform security checks at every stage of the application pipeline, analyse code for vulnerabilities before deployment, utilise Software Composition Analysis (SCA) tools to prevent issues in third-party libraries, and use a Web Application Firewall (WAF) to prevent OWASP Top 10 vulnerabilities.
Our Infrastructure
Authentication
Authentication is performed over encrypted connections. Reqi supports integration with any Identity Provider that supports OIDC or SAML, including Google SSO and Microsoft. A strong password policy prevents easily guessable or brute-forceable passwords.
Encryption
All data is encrypted at rest with AES-256 and in transit with TLS 1.2 minimum. This ensures end-to-end security of data sent between applications over the Internet and maximum protection for stored data.
Payment Security
Reqi does not store credit or debit card information on our servers. We use Stripe, a PCI-compliant service that securely stores sensitive payment data — keeping your financial information separate and protected.
Disaster Recovery
All assets are zone-redundant with automatic failover configured. The customer data Recovery Time Objective (RTO) is 4–5 minutes. Critical patches are applied within 48 hours of release.
Incident Response
In case of any outage, it is reported immediately. Our first priority is identifying the compromised access, isolating or containing the damage, eradicating the offending component, and putting measures in place to prevent the incident from recurring.
Patch management: We maintain an extensive patch management procedure. Critical patches are applied within 48 hours of their release to minimise exposure to known vulnerabilities.
Have Security Questions?
Reqi is a secure and reliable choice for requirements management. Our support team is available to address any additional security concerns or compliance questions specific to your organisation.
Contact Us